Search results
The DOL’s New Guidance for AI and its Impact in the Workplace | JD Supra
JD Supra· 2 days agoIn this monthly series brought to you CDF's Wage and Hour Taskforce, we will delve into the WHD's recent release of a Field Assistance Bulletin relating to Artificial Intelligence in the workplace ...
What is Risk-Based Vulnerability Management (RBVM)?
SearchSecurity.com· 5 days agoRisk-based vulnerability management (RBVM) is an approach to identifying and addressing security vulnerabilities in an organization's IT environment that prioritizes remediating vulnerabilities ...
DOL Issues Guidance on Workplace AI | JD Supra
JD Supra· 4 days agoAmong other things, the DOL guidance indicates that employers may be held liable for the unlawful conduct of AI systems or tools they use, even if those systems or tools were designed by a third-party ...
Council Post: Unlocking Productivity (And Profitability) In The Era Of Invisible Digital Work
Forbes· 3 days agoIn fact, a staggering 83% of CxOs admit they struggle to measure the ROI of workforce investments....
ROSPaCe: Intrusion Detection Dataset for a ROS2-Based Cyber-Physical System and IoT Networks -...
Nature· 24 hours agoThe discussion is divided into three parts. First, we define our system and its setting, including the monitoring system, the data collection method, and the attacks towards ...
Synchronizing IT And Operations Technology (OT): A Framework
Forbes· 2 days agoThis article provides a high-level overview of key considerations for technology leaders navigating...
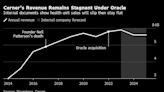
Oracle’s $28 Billion Cerner Health Tech Bet Sputters With Lost Customers and Slipping Sales
Bloomberg via Yahoo Finance· 2 days ago(Bloomberg) -- When Oracle Corp. spent $28 billion two years ago to acquire electronic-records...
The Double-Edged Impact of AI Compliance Algorithms on Whistleblowing | JD Supra
JD Supra· 24 hours agoAs the implementation of Artificial Intelligence (AI) compliance and fraud detection algorithms within corporations and financial institutions continues to grow, it is crucial to consider how ...
How to Catch a Cheater: 11 Ways Technology Reveals Secrets
HowStuffWorks via Yahoo News· 3 days agoTechnology can help cheaters connect with paramours -- but it can also leave a trail that gets them caught. How does our connection to the digital world make it easier to expose infidelity?
How Can Businesses Defend Themselves Against Cyberthreats?
TechRepublic· 18 hours agoToday, all businesses are at risk of cyberattack, and that risk is constantly growing. Furthermore,...